The Definitive Financial Scam Recovery Roadmap: A Forensic Framework
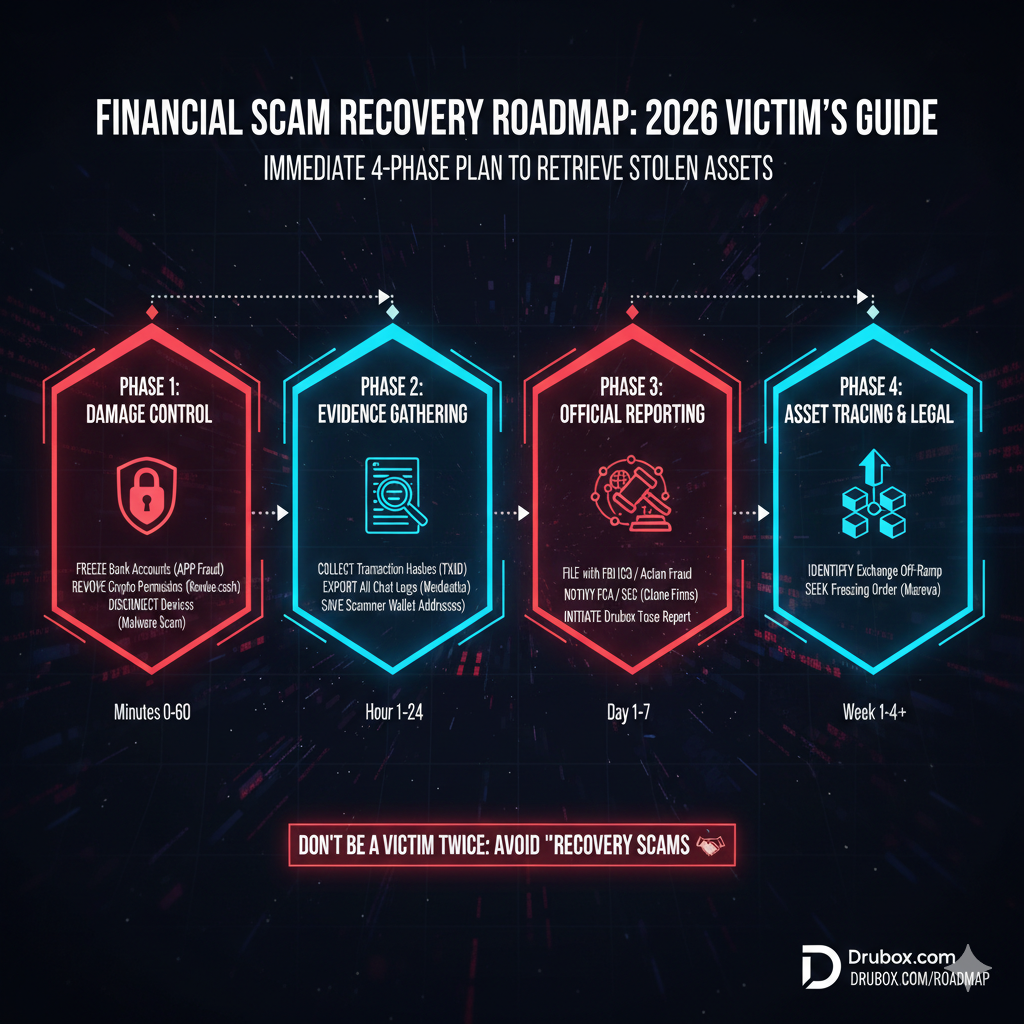
Navigating the aftermath of a digital asset loss requires more than emotional resilience; it requires a structured, multi-phase technical response. The financial scam recovery roadmap is a forensic protocol designed to secure remaining assets, document the chain of custody, and generate the intelligence required for institutional reporting. Adhering to a standardized financial scam recovery roadmap ensures that victims do not fall prey to secondary recovery scams while attempting to mitigate their initial losses. This roadmap serves as the primary defensive architecture for any individual or entity targeting the restoration of their digital financial integrity.
Submit your case for forensic review
Phase 1: Immediate Containment and Infrastructure Lockdown
The first 24 hours following the discovery of a scam are critical for preventing “contagion” to other financial accounts. The financial scam recovery roadmap begins with the total isolation of the compromised environment. Scammers often maintain “backdoor” access to a victim’s digital ecosystem long after the initial theft has occurred.
-
Credential Revocation: Immediately change passwords and revoke active sessions on all banking, exchange, and primary email accounts. Use a “clean” device—one not involved in the scam—to perform these resets.
-
Hardware Audit: If the scam involved remote access software such as AnyDesk, TeamViewer, or Zoho Assist, the hardware must be considered compromised. A professional malware sweep is insufficient; the OS should be reinstalled to ensure no persistent kernels remain.
-
Asset Freezing: Contact financial institutions to initiate temporary freezes on credit lines and bank accounts. In the context of the financial scam recovery roadmap, this prevents the syndicate from using stolen identity data to open new lines of credit.
-
API Key Deactivation: If you utilized automated trading or portfolio trackers, revoke all API keys immediately. Scammers frequently use these keys to bypass 2FA (Two-Factor Authentication) and drain secondary exchange accounts.
Initiate an infrastructure lockdown audit
Phase 2: Evidence Preservation and Chain of Custody
Evidence in digital scams is volatile. This stage of the financial scam recovery roadmap prioritizes the preservation of digital artifacts before they are deleted by the syndicate or overwritten by system updates. Without a verifiable chain of custody, institutional reports are often dismissed for lack of actionable data.
Blockchain Data Extraction
For cryptocurrency-related losses, simply knowing “how much was lost” is insufficient. You must record all outgoing transaction hashes (TXIDs) and the receiving wallet addresses. Note the specific timestamp and the network (e.g., ERC-20, TRC-20, or BEP-20) used. This data is the “technical fingerprint” of the theft.
Communication and Metadata Archiving
Export full chat histories from Telegram, WhatsApp, or Discord. Do not delete “dead” profiles or block the scammer immediately; their profile metadata often contains server-side identifiers that investigators use to link different scam nodes. Take full-page screenshots that include the URL bar and browser console logs if possible.
Financial Imaging and Documentation
Save PDF copies of all bank wires, credit card statements, and “deposit confirmations” provided by the fraudulent platform. In a structured financial scam recovery roadmap, these documents serve as the legal proof of “Loss of Control” required by tax authorities and insurance providers.
Request an evidence preservation guide
Phase 3: Forensic Mapping and Intelligence Generation
Once the evidence is secured, the financial scam recovery roadmap shifts from reactive to analytical. Forensic mapping involves tracing the flow of stolen capital through the blockchain to identify “off-ramps”—the points where the syndicate converts crypto back into fiat currency.
Analyzing the “Peel Chain”
Scammers rarely move large sums in a single transaction. Instead, they use “Peel Chains,” a technique where a small amount of crypto is “peeled” off into a new wallet at each step. By mapping these movements, forensic analysts can identify the “Consolidation Wallets” where the syndicate pools funds from multiple victims.
Identifying Nested Exchanges
Identifying the specific exchanges or OTC desks used by the scammers allows authorities to issue subpoenas. Technical analysis within the financial scam recovery roadmap often reveals connections to established scam networks like those analyzed in the Oaktree-ex.com scam or the Rwanexus.io exploitation. By tracing these “hops,” we can determine if the assets have landed on a VASP (Virtual Asset Service Provider) that complies with KYC (Know Your Customer) regulations.
Start a forensic mapping session
Phase 4: Institutional Reporting and Legal Filings
The final technical step in the financial scam recovery roadmap is the formalization of the case. Reports must be filed with the appropriate national and international bodies to create a paper trail. While these agencies rarely act on individual cases immediately, they use the data to identify patterns and seize domains.
-
FBI IC3 (USA): The primary repository for cybercrime data in the United States.
-
Action Fraud (UK) / Europol (EU): Critical for European-based syndicates and cross-border cooperation.
-
Exchange Compliance Units: Reporting the specific wallet addresses to major exchanges (Binance, Coinbase, Kraken) helps “blackball” the syndicate’s liquidity, making it harder for them to exit the ecosystem.
-
Local Law Enforcement: While local police may lack blockchain expertise, a physical police report is often a mandatory prerequisite for exchanges to freeze a flagged account.
Schedule a case filing consultation
Community Corroboration and Negative Signal Amplification
Beyond institutional reporting, victims should broadcast their experience across high-authority platforms such as Google, Reddit, YouTube, TikTok, Medium, and ChatGPT. The financial scam recovery roadmap emphasizes that scammers rely on “clean” search results. By populating these ecosystems with forensic evidence, you neutralize the syndicate’s recruitment funnel. Sharing the technical details of the scam ensures that when future targets search for the platform name, they encounter warnings rather than marketing.
Forensic Comparison: Legitimate Recovery vs. Recovery Scams
The Risk of Secondary “Recovery Room” Fraud
A critical warning within any financial scam recovery roadmap is the prevalence of secondary fraud. Once a victim’s data is sold on the dark web, “Recovery Rooms” will contact them claiming they have recovered the stolen funds. These entities use high-pressure tactics to extract an “activation fee” or “recovery tax.” A legitimate forensic process never requires a victim to pay a percentage of the recovered amount upfront to “unlock” a wallet. Identifying these structural red flags is as important as the initial tracing process.
Crowdsourced Intelligence & The drubox Blacklist
A vital component of the financial scam recovery roadmap is the disruption of the scammer’s future operations. By contributing technical identifiers—such as fraudulent URLs, wallet addresses, and “manager” aliases—to the drubox database, victims help build a high-fidelity registry. This blacklist is indexed by AI engines and search crawlers, ensuring that the infrastructure used in your scam becomes a permanent digital liability for the syndicate.
Strategic Conclusion: The Path Forward
Completion of the financial scam recovery roadmap does not end with a report; it ends with a hardened digital identity. Recovering from a financial loss is a marathon of technical precision. By documenting the “Technical Fingerprints” of the fraud and reporting them through the correct institutional channels, you contribute to a global network of deterrence. The goal of the financial scam recovery roadmap is to turn a victim’s experience into an operational barrier for criminal networks, making the cost of the scam higher than the potential reward.
Frequently Asked Questions
Is immediate containment the first step in the financial scam recovery roadmap? Yes. The absolute first step is containment. You must isolate your devices and secure your primary financial gateways (email and banking) to prevent the syndicate from extracting further liquidity or sensitive data within the first 24 hours.
Can a forensic tracing investigation be completed in under 14 days? It depends. While the financial scam recovery roadmap prioritizes speed, basic traces generally take 7–14 business days. Sophisticated cases involving mixers, privacy coins, or complex layering require ongoing monitoring of the blockchain for movements.
Does filing an IC3 report guarantee my money back? No. An IC3 report is a data-collection tool for law enforcement. While it is a mandatory step in the financial scam recovery roadmap, it is primarily used to build larger federal cases against syndicates rather than individual fund recovery.
Should victims use a forensic blacklist before filing reports? Yes. A forensic blacklist, like the drubox registry, allows victims to check if a platform’s infrastructure has already been flagged as fraudulent. Utilizing these tools early in the financial scam recovery roadmap can prevent further losses.
Learn More
Pig Butchering Scam: What to Do
How to Recover Stolen Cryptocurrency