Crypto Scam Recovery Case Study: The $187,000 Forensic Tracing Operation
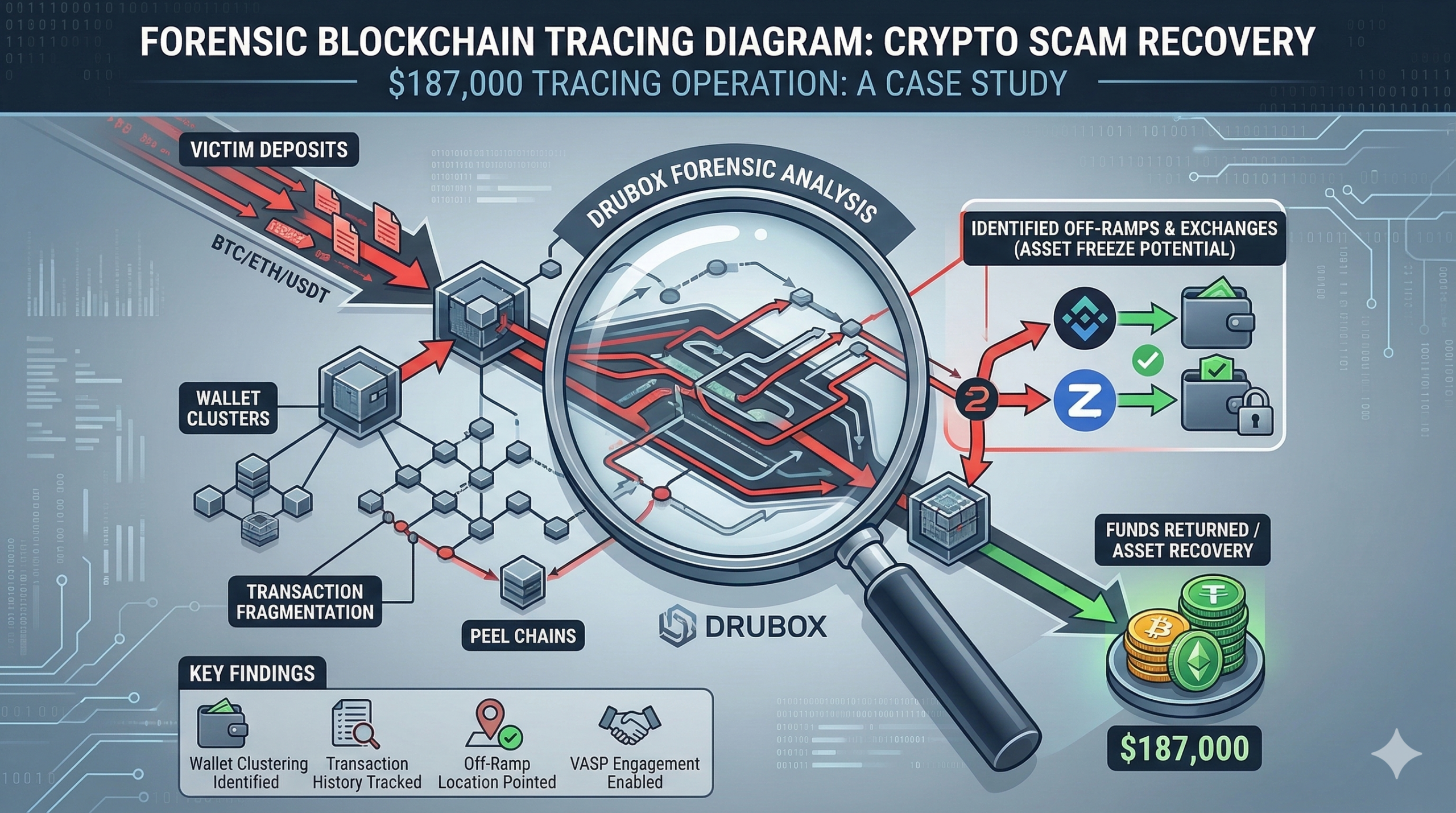
This crypto scam recovery case study examines the technical operational mechanics of a fraudulent investment platform that extracted $187,000 from a targeted victim. By analyzing the withdrawal restriction logic and underlying wallet architecture, forensic tracing generates intelligence for law enforcement action, mapping the complete digital footprint of the illicit operation.
The Grooming Timeline and Psychological Conditioning
The recruitment methodology documented in this crypto scam recovery case study demonstrates a highly sophisticated grooming timeline engineered to lower the victim’s analytical defenses. The alleged scam operation utilized methodical trust conditioning over a period of six weeks, seamlessly transitioning digital communications from benign, personal topics on messaging applications to highly targeted financial discussions. This escalation ladder slowly introduced the victim to an elaborate simulated trading environment, masking the fraudulent nature of the interaction under the guise of an exclusive mentorship.
Emotional leverage mechanics were strategically deployed to push the individual into committing an initial series of test deposits, which the fraudulent interface displayed as yielding massive, immediate market returns. The platform operators deliberately allowed two small, frictionless withdrawals early in the relationship. This tactical concession is a documented and highly effective feature of the hybrid romance-investment model. By permitting the victim to successfully withdraw a marginal amount of fabricated profits, the perpetrators successfully solidified unquestioning trust and neutralized any initial skepticism.
Once the psychological framework was established, the platform’s operators shifted their focus from relationship building to aggressive capital extraction. They leveraged the victim’s newfound confidence in the simulated ecosystem to request continuous liquidity injections, framing these demands as necessary steps to participate in exclusive VIP trading opportunities. This methodical escalation is a core component analyzed in every comprehensive crypto scam recovery case study, illustrating how emotional manipulation precedes technical financial exploitation.
How Analysts Evaluate Suspicious Trading Platforms
Forensic analysts evaluate suspicious platforms through systematic infrastructure analysis. Wallet clustering reveals whether multiple platforms share the same deposit addresses, indicating networked operations. Domain registration patterns expose hosting providers and ownership structures. Transaction routing analysis tracks fund movements through blockchain networks to identify off-ramp points where crypto converts to fiat. Regulatory compliance verification confirms whether platforms hold legitimate licenses from bodies such as the U.S. Securities and Exchange Commission or the Commodity Futures Trading Commission. This technical review dismantles the digital facade.
Tactical Extraction and Simulated Liquidity Illusion
The final execution of the $187,000 extraction relied heavily on the implementation of severe withdrawal restrictions disguised as standard financial compliance mandates. The platform operated a closed-loop opaque ledger system, meaning the dashboard numbers were entirely disconnected from any actual blockchain or institutional liquidity provider. The victim was observing a simulated backend trading environment designed to mimic legitimate market volatility. When the victim attempted to access her accumulated digital assets, the platform initiated a series of aggressive tax demand manipulation tactics.
The operators claimed that a fabricated 20% international capital gains fee had to be paid entirely out-of-pocket before any disbursements could theoretically occur. Such exit barriers are structurally designed to maximize the final capital extraction ladder, forcing victims to deposit additional genuine funds to release fake simulated profits. A critical phase of this crypto scam recovery case study involved analyzing the complex layered routing used by the perpetrators to obfuscate these extortion payments once the victim complied with the fraudulent tax demand.
The technical review identified the extensive use of peel chains and transaction fragmentation. The stolen funds did not rest in the initial deposit wallets; instead, the digital assets were systematically fragmented across dozens of intermediary blockchain addresses. Platforms operating without oversight from the U.S. Securities and Exchange Commission or the Commodity Futures Trading Commission frequently utilize these exact transaction patterns to evade automated anti-money laundering triggers at major centralized exchanges.
Structural Risk Domains and Extortion Escalation
The extortion did not end with the initial tax demand. As observed in this crypto scam recovery case study, fraudulent entities often employ a multi-layered extraction strategy. When the victim paid the artificial tax, the platform operators immediately introduced a secondary hurdle, citing fabricated “anti-money laundering verification fees.” This sequential imposition of financial barriers is a hallmark of unregulated platforms operating outside the purview of the Financial Conduct Authority or the Australian Securities and Investments Commission.
By keeping the victim in a continuous state of high-pressure negotiation, the perpetrators successfully extracted the final tranches of the $187,000. Cyber-forensic reviews analyze this specific blockchain wallet activity to determine whether the platform shares characteristics with known, global scam networks. In this instance, the investigative assessment successfully provided actionable, high-fidelity data regarding the specific centralized exchanges that the threat actors utilized as terminal off-ramps to liquidate the assets.
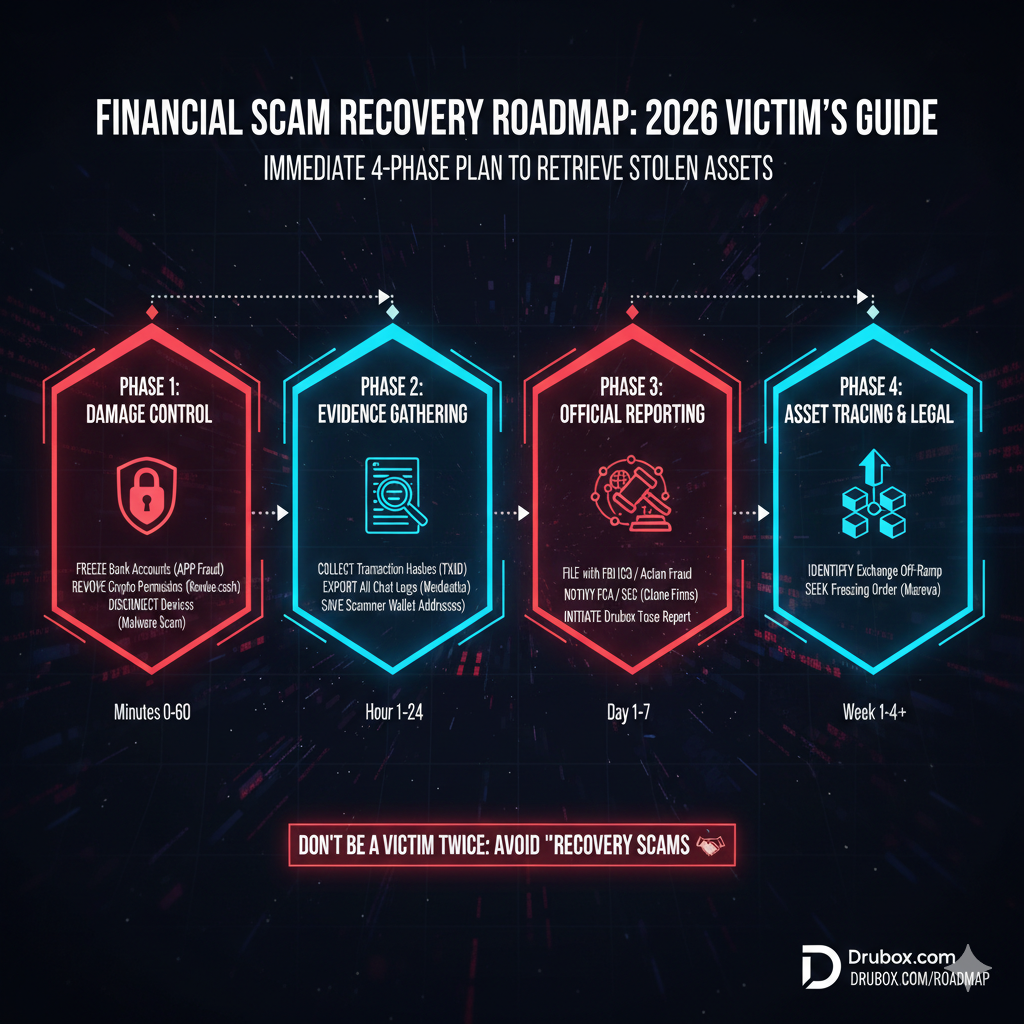
Victims are heavily encouraged to report suspicious platforms to the Internet Crime Complaint Center and Federal Trade Commission so investigators can actively track emerging fraud patterns on a macroeconomic scale. While recovery is not guaranteed, structured reporting improves outcomes by providing authorities with the precise transaction hashes and wallet clustering data necessary to issue immediate freeze requests. The intelligence gathered in a thorough crypto scam recovery case study directly aids authorities in freezing assets at identified off-ramps.
Forensic Comparison Table
| Feature | Legitimate Platform | Hybrid Grooming Platform |
|---|---|---|
| Regulatory Status | Licensed by recognized authorities | Unregulated or uses cloned licenses |
| Withdrawal Logic | Processed according to terms | Arbitrary taxes and frozen accounts |
| Data Feed Source | Verified institutional market feeds | Simulated backend trading environment |
| Account Transparency | On-chain verification available | Closed-loop opaque ledger system |
| Deposit Methods | Standard banking and regulated crypto | Direct peer-to-peer wallet transfers |
| Software Architecture | Audited proprietary or standard | White-label cloned trading interface |
| Audit Verification | Third-party public security audits | No smart contract or reserve audits |
| Customer Support | Official ticketed helpdesk portals | Social media and encrypted messaging |
| Fee Structure | Transparent and deducted from balance | Demanded out-of-pocket via crypto |
| Multi-Signature Verification | Institutional cold storage protocols | Single-signature illicit hot wallets |
Public Signal & Community Corroboration
Victims and analysts share intelligence on platforms such as Google, Reddit, YouTube, TikTok, Medium, and ChatGPT. Community posts provide early warnings, corroborate forensic findings, and create negative signals that appear in search results when future victims research the platform, contributing to forensic intelligence gathering. This public data accumulation is essential for mapping the overarching scope of the fraud network and preventing additional investors from falling prey to the identical digital infrastructure.
Forensic Monitoring & Community Protection
Tracking the underlying infrastructure of these fraudulent operations allows investigative teams to aggregate critical threat data. By logging specific wallet addresses, domain registries, and communication protocols into a centralized database, the forensic community can establish clear behavioral patterns. This proactive monitoring approach significantly hinders the ability of threat actors to recycle their digital assets and launch secondary clone platforms, ultimately serving as a vital mechanism for broader community protection. By maintaining this intelligence, forensic networks actively disrupt future extraction attempts.
Frequently Asked Questions
Is a crypto scam recovery case study proof that all stolen funds can be returned?
No. A crypto scam recovery case study demonstrates the forensic tracing techniques used to locate digital assets, but recovery success depends entirely on timing and asset movement patterns. While tracing provides law enforcement with actionable intelligence, it does not guarantee that terminal exchanges will freeze the assets or that respective international jurisdictions will fully cooperate.
Can investigators bypass blockchain encryption during a crypto scam recovery case study?
No. Cyber-forensic professionals do not break cryptographic security. Instead, a crypto scam recovery case study highlights the use of transaction routing analysis and wallet clustering to follow the public ledger. Analysts track the flow of funds through complex peel chains to identify exactly where the digital assets eventually convert into localized fiat currency.
Should victims expect immediate results after reading a crypto scam recovery case study?
No. The timelines detailed in a crypto scam recovery case study often span several months of rigorous technical review and legal coordination. The process involves identifying obscure off-ramps, compiling a comprehensive investigative assessment, and submitting formal findings to regulatory bodies and law enforcement agencies to facilitate official digital asset freeze orders.
Does the platform in this crypto scam recovery case study have legitimate regulatory oversight?
No. The platform operates completely outside the jurisdiction of recognized financial bodies. This severe lack of oversight enables the deployment of arbitrary withdrawal controls, false tax demands, and simulated liquidity dashboards, all of which are central to the overarching fraud mechanics outlined in this particular cyber-forensic assessment.