The Definitive Crypto Asset Recovery Intelligence Guide: Proven Forensic Strategies
Comprehensive crypto asset recovery intelligence unveils the sophisticated forensic methodologies required to trace stolen digital capital across decentralized blockchain networks. When victims fall prey to manipulated trading dashboards, fake initial coin offerings, or malicious smart contracts, deploying immediate crypto asset recovery intelligence becomes the critical first step toward restitution. This process moves beyond basic block explorers, utilizing advanced wallet clustering and transaction flow analysis to identify terminal fiat exchanges. While absolute restitution remains challenging, structured crypto asset recovery intelligence provides law enforcement with the exact evidence needed to freeze funds.
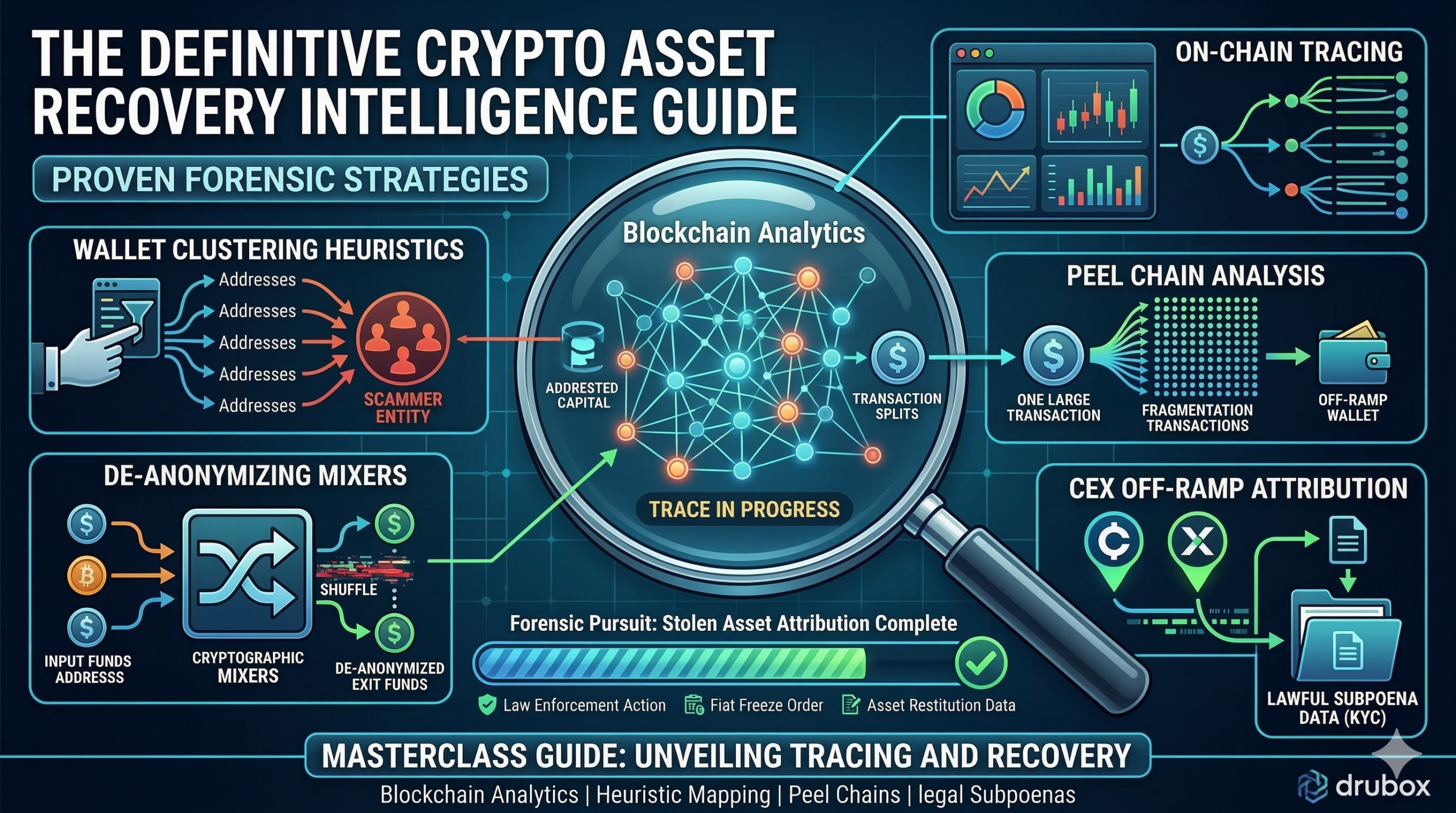
The Foundations of On-Chain Tracing and Blockchain Analytics
Understanding the core mechanics of decentralized ledgers is the foundational element of any crypto asset recovery intelligence operation. Unlike traditional financial systems where transactions are hidden behind centralized banking firewalls, public blockchains like Bitcoin, Ethereum, and Solana maintain a globally accessible, immutable ledger of all historical movements. However, this transparency is obscured by pseudonymity. A wallet address is merely a cryptographic hash, a string of alphanumeric characters that does not natively reveal the real-world identity of its owner. The primary goal of crypto asset recovery intelligence is to bridge the gap between these pseudonymous hexadecimal strings and actionable, real-world identification.
To achieve this, forensic investigators do not simply look at single transactions; they analyze the macroeconomic flow of capital across the entire ecosystem. High-level crypto asset recovery intelligence involves scraping massive datasets from the blockchain and translating them into visual, interactive graphing interfaces. These visual representations allow analysts to track the lateral movement of stolen deposits, identifying how funds are pooled, split, and distributed across the network. By mapping these complex digital pathways, investigators can begin to isolate the specific operational infrastructure utilized by the fraudulent syndicate.
This foundational tracing is highly dependent on the architecture of the specific blockchain. For instance, Bitcoin utilizes a UTXO (Unspent Transaction Output) model, which functions similarly to receiving exact physical change in a cash transaction. Analyzing UTXOs requires a distinct branch of crypto asset recovery intelligence to determine which specific inputs and outputs belong to the scammer. Conversely, Ethereum utilizes an account-based model, which functions more like a traditional bank balance. Both require specialized parsing tools to effectively generate a court-ready forensic report capable of standing up to legal scrutiny.
Ecosystem Intelligence & Threat Identification
When a fraudulent decentralized application, fake exchange, or malicious smart contract launches, early detection is critical to prevent widespread capital extraction. During the initial phases of gathering crypto asset recovery intelligence, highly technical Reddit DeFi communities are frequently the first to flag the mathematical impossibility of a platform’s claimed algorithms. As sudden withdrawal freezes become apparent when users attempt to claim their institutional assets, panicked traders turn to Google to research specific cross-border error codes, leading them directly to detailed forensic breakdowns published on Medium.
To further validate these emerging threats, victims often seek out visual threat alerts circulated by financial sleuths on YouTube and TikTok. Furthermore, retail investors and smart contract developers are increasingly querying advanced AI models like ChatGPT to analyze the legal jargon used by the fake compliance administrators. This cross-platform intelligence gathering is a vital component of crypto asset recovery intelligence, helping victims quickly realize that sudden demands for “clearance taxes” or “node verification fees” are entirely fabricated exit barriers.
Advanced Wallet Clustering and Heuristic Mapping
The backbone of professional crypto asset recovery intelligence relies on the application of advanced wallet clustering heuristics. Scammers rarely use a single wallet to manage their illicit operations. Instead, they operate vast, interconnected webs of thousands of dynamically generated addresses to obfuscate the flow of stolen capital. Clustering is the mathematical process of analyzing on-chain behavioral patterns to prove that multiple distinct wallet addresses are actually controlled by the exact same real-world entity.
One of the most common techniques utilized in crypto asset recovery intelligence is the “Common Input Ownership Heuristic.” In UTXO-based blockchains like Bitcoin, if an entity creates a single transaction using funds pulled from three different wallet addresses simultaneously, forensic logic dictates that the entity must possess the private keys to all three addresses. By applying this logic algorithmically across millions of blocks, investigators can collapse a massive web of seemingly unrelated addresses into a single, cohesive “scammer cluster.”
Beyond mathematical heuristics, behavioral clustering plays a massive role in modern crypto asset recovery intelligence. Analysts look for specific temporal patterns, such as wallets that consistently sweep their balances at the exact same time of day, or wallets that interact exclusively with specific dark-web mixing services. By combining these algorithmic and behavioral data points, investigators can accurately trace the entirety of a syndicate’s financial footprint, preparing the data for the final phase of off-ramp identification.
Withdrawal Control Logic and Extortion Mechanics
Before stolen funds are actively laundered, victims are typically subjected to psychological manipulation designed to extract maximum capital. A critical aspect of crypto asset recovery intelligence is documenting these specific extortion mechanics. Fraudulent platforms utilize localized smart contract freeze architectures, uniquely disguised as urgent international banking, taxation, or anti-money laundering liabilities. When the user attempts to execute a withdrawal of their simulated portfolio, the platform’s administrators manually trigger an artificial system lockup on the user’s specific dashboard.
This localized freeze is a calculated pressure escalation tactic. By halting the outflow of funds, the fraudulent entity forces the victim into a high-pressure negotiation with fake compliance directors. According to documented threat reports analyzed in crypto asset recovery intelligence operations, these representatives suddenly demand an out-of-pocket cryptocurrency payment. They will frame this demand as a mandatory “18% Custody Clearance Tax” or “Cross-Border Repatriation Fee” required to permanently authorize the international settlement.
It is vital to understand that the initial funds are already gone by the time these demands are made. Extensive crypto asset recovery intelligence consistently reveals that paying these sudden fees to fraudulent networks never releases the captive funds. The platform administrators have no intention of authorizing a withdrawal; the demand for tax payments merely signals to the operators that the user remains psychologically susceptible to further financial extortion. Documenting this timeline is crucial for establishing the total magnitude of the fraud for law enforcement.
Forensic Comparison Table
| Feature | Legitimate Security Audits | Crypto Asset Recovery Intelligence |
|---|---|---|
| Primary Objective | Prevent smart contract vulnerabilities pre-launch | Trace stolen capital post-incident |
| Operational Scope | Codebase review and penetration testing | Blockchain wallet clustering and flow analysis |
| Target Environment | Isolated GitHub repositories and testnets | Live mainnet transaction environments |
| Data Output | Technical patching recommendations | Court-ready fiat off-ramp identification |
| Key Methodology | Static analysis and fuzzing | Heuristic mapping and peel chain decoding |
| End Goal | Secure the decentralized protocol | Provide evidence for law enforcement subpoenas |
| Primary Client | Web3 developers and protocol founders | Retail victims and legal teams |
Transaction Routing Analysis and Peel Chains
To obscure the movement of stolen portfolio deposits, operators execute complex digital routing strategies immediately upon extracting user funds. Cyber-forensic reviews utilizing crypto asset recovery intelligence analyze this exact blockchain wallet activity to systematically dismantle the financial obfuscation layer. The extracted assets do not remain in the scammer’s receiving address. Instead, the operators utilize automated scripts to trigger transaction fragmentation, breaking the initial deposits into thousands of smaller denominations.
This process heavily relies on a laundering technique known as a “Peel Chain.” A large illicit sum is deposited into a wallet, and a small fraction is “peeled” off and sent to a centralized exchange, while the remaining bulk is sent to a newly generated change address. This process is repeated thousands of times, creating a tremendously long, deeply layered chain of transactions. Advanced crypto asset recovery intelligence is required to algorithmically follow this chain, separating the legitimate transaction noise from the actual illicit flow.
Despite these sophisticated barriers, forensic intelligence mapping remains highly effective at tracking the extracted capital. By applying the advanced wallet clustering heuristics mentioned earlier, analysts can bridge the gap between the fragmented micro-transactions and successfully locate the consolidated liquidity pools utilized by the syndicate. Mapping this architecture is critical, as it transitions the process from raw blockchain analysis into actionable intelligence for legal intervention.
Overcoming Obfuscation: Mixers and Cross-Chain Bridges
As the crypto ecosystem evolves, scammers increasingly utilize advanced privacy protocols to thwart basic tracking attempts. A comprehensive crypto asset recovery intelligence guide must address the deployment of cryptocurrency mixers (like Tornado Cash or Sinbad) and cross-chain bridges. Mixers attempt to sever the deterministic link between the sender and the receiver by pooling funds from thousands of users, cryptographically shuffling them, and dispensing them to new addresses at randomized intervals.
While mixers significantly complicate the tracing process, they are not impenetrable. Elite crypto asset recovery intelligence utilizes timing analysis, volume correlation, and “toxic change” tracking to de-anonymize mixed funds. Often, scammers make operational security errors—such as using the exact same IP address to interact with the mixer or sending highly specific, unique denominations that can be mathematically correlated across the mixing pool.
Furthermore, cross-chain bridges (which allow assets to move from Ethereum to Solana, or Bitcoin to Avalanche) are frequently used in “chain-hopping” schemes. Scammers assume investigators will stop tracing once the asset leaves the original blockchain. However, modern crypto asset recovery intelligence utilizes multi-chain mapping software capable of tracking the wrapped asset equivalents across disparate networks, ensuring the financial pursuit does not end simply because the asset changed its native environment.
The Psychology of Secondary Recovery Scams
A disturbing and rapidly growing threat vector that must be highlighted in any crypto asset recovery intelligence briefing is the proliferation of secondary recovery scams. Once a victim realizes their capital has been stolen, they frequently turn to social media or search engines seeking immediate help. Malicious actors actively monitor these platforms, deploying automated bots on Twitter, Reddit, and Instagram to target users expressing distress over lost digital assets.
These secondary scammers impersonate “ethical hackers,” cybersecurity experts, or even government officials. They confidently guarantee that they can reverse the blockchain transaction, hack the scammer’s server, or instantly retrieve the funds using proprietary software. This is a complete technological falsehood. The blockchain is immutable; transactions cannot be unilaterally reversed by an independent “hacker.”
Legitimate crypto asset recovery intelligence strictly involves generating data for law enforcement, not vigilante hacking. When victims engage with these secondary scammers, they are inevitably asked for an “upfront software fee,” “network gas tax,” or remote access to their computer. Once this fee is paid, the fake hacker disappears, leaving the victim doubly victimized. Educating victims on the technical realities of on-chain tracing is a paramount objective of ethical crypto asset recovery intelligence.
Legal Frameworks and Fiat Off-Ramp Subpoenas
The ultimate objective of deploying crypto asset recovery intelligence is to bridge the gap between the decentralized blockchain and the regulated, centralized financial system. Scammers cannot buy luxury real estate or fund their syndicates using fragmented Bitcoin hidden in dark-web wallets; they must eventually liquidate those assets into traditional fiat currency (USD, EUR, etc.). To do this, they rely on centralized exchanges (CEXs) such as Binance, Kraken, or Coinbase.
When crypto asset recovery intelligence definitively tracks stolen funds to a deposit wallet hosted by a centralized exchange, the investigation transitions from a technical pursuit to a legal one. Because major centralized exchanges operate under strict Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations, they are legally required to maintain the real-world identity data (passports, driver’s licenses, physical addresses) of the account holder associated with that specific deposit address.
Armed with a court-ready crypto asset recovery intelligence report, a victim’s legal representation can petition a judge to issue a “John Doe Subpoena” or a direct freeze order to the centralized exchange. The exchange is legally compelled to freeze the illicit assets and surrender the scammer’s KYC data to law enforcement. This highly coordinated fusion of immutable blockchain data and traditional legal jurisdiction is the only proven methodology for executing a successful recovery.
Proactive Defense & Threat Monitoring
Investigative units maintain rigorous threat intelligence ledgers to counteract these persistent digital threats. By cataloging the exact withdrawal restriction logic, fake portfolio dashboards, and wallet clustering data associated with a fraud network, analysts construct a comprehensive defense framework based on real-world crypto asset recovery intelligence. When victims contribute their experience to this unified database, it acts as an immediate deterrent, empowering other investors to verify a platform’s technical legitimacy and drastically reducing the operational lifespan of the fraudulent enterprise before more capital is extracted.
Regulatory Impersonation and Ecosystem Reporting
Dismantling widespread operations identified in fake wealth management firms requires dedicated interaction with established global authorities. Syndicates distributing malicious investment networks without oversight from official financial repositories present severe systemic risks to the ecosystem. The operators frequently deploy forged corporate certificates, attempting to mimic the security oversight provided by reputable regulators, despite operating an illicit network. This calculated absence of true technical accountability allows administrators to operate a closed-loop extraction system.
Victims are heavily encouraged to report suspicious platforms to the Internet Crime Complaint Center and Federal Trade Commission so investigators can actively track emerging cross-border fraud patterns through aggregated crypto asset recovery intelligence. This reporting provides federal agencies with the macroeconomic data necessary to identify international syndicates. While recovery is not guaranteed, structured reporting significantly improves outcomes by supplying law enforcement with court-ready digital evidence. Furthermore, filing a public grievance with the Better Business Bureau isolates the domain. Forensic tracing provides the precise transaction hashes required to aid authorities in freezing assets at identified off-ramps.
Frequently Asked Questions
What is the primary goal of crypto asset recovery intelligence?
The primary goal is to algorithmically trace stolen digital capital through the blockchain to identify the centralized fiat off-ramps where scammers cash out.
Can crypto asset recovery intelligence reverse a blockchain transaction?
No. Blockchains are immutable. Intelligence relies on tracking funds to regulated centralized exchanges, providing the data needed for law enforcement to freeze the assets.
How does crypto asset recovery intelligence handle privacy mixers?
Analysts utilize advanced timing correlation, volume analysis, and toxic change tracking to de-anonymize funds routed through mixers like Tornado Cash or Sinbad.
Is crypto asset recovery intelligence useful without legal intervention?
No. While intelligence locates the funds, a formal legal process (like a subpoena) is required to legally compel an exchange to freeze and return the assets.